- Cisco Easy Vpn Configuration
- Cisco Easy Vpn Remote
- Cisco Vpn Client 64 Bit Windows 10
- Cisco Easy Vpn Server
- Cisco Easy Vpn Client
- Cisco Easy Vpn Setup
Cisco Easy VPN Remote routers are more similar to Cisco 3002 hardware clients. Both support client and network extension modes, as shown in Figure 18-2. If you recall from Chapter 3, in client mode, the Easy VPN Remote is assigned a single internal IP address; all devices behind the Remote have PAT performed on them by the Remote to send their. The Easy VPN Remote feature minimizes configuration requirements at remote locations by allowing Cisco IOS routers, Cisco ASA 5505 Adaptive Security Appliances, Cisco PIX Security Appliances, and the Cisco VPN Client to receive security policies upon a VPN tunnel connection from a Cisco Easy VPN Server. Cisco Easy VPN Remote routers are more similar to Cisco 3002 hardware clients. Both support client and network extension modes, as shown in Figure 18-2. If you recall from Chapter 3, in client mode, the Easy VPN Remote is assigned a single internal IP address; all devices behind the Remote have PAT performed on them by the Remote to send their. The main advantage of Easy VPN is that IPSec policies are centrally managed on the server (Head end router providing IPSec feature) and are pushed to client devices. This policy push is known as Mode Configuration. This requires minimum configuration on the end-user side. The Cisco VPN Client is available for both 32bit and 64bit Windows operating systems. To download the latest Cisco VPN Client, simply visit our download section and look for our new Cisco Tools category! FREE Hyper-V & VMware Backup. Bandwidth Monitor. Free PatchManager.
Table Of Contents
Configuring a VPN Using Easy VPN and an IPSec Tunnel
The Cisco 870 series routers support the creation of Virtual Private Networks (VPNs).
Cisco routers and other broadband devices provide high-performance connections to the Internet, but many applications also require the security of VPN connections which perform a high level of authentication and which encrypt the data between two particular endpoints.
Two types of VPNs are supported—site-to-site and remote access. Site-to-site VPNs are used to connect branch offices to corporate offices, for example. Remote access VPNs are used by remote clients to log in to a corporate network.
The example in this chapter illustrates the configuration of a remote access VPN that uses the Cisco Easy VPN and an IPSec tunnel to configure and secure the connection between the remote client and the corporate network. Figure 6-1 shows a typical deployment scenario.
Note The material in this chapter does not apply to Cisco 850 series routers. Cisco 850 series routers do not support Cisco Easy VPN.
Figure 6-1 Remote Access VPN Using IPSec Tunnel
Remote, networked users | |
2 | VPN client—Cisco 870 series access router Jriver media center 23 mac. |
Router—Providing the corporate office network access | |
4 | VPN server—Easy VPN server; for example, a Cisco VPN 3000 concentrator with outside interface address 210.110.101.1 |
Corporate office with a network address of 10.1.1.1 | |
6 | IPSec tunnel |
Cisco Easy VPN
The Cisco Easy VPN client feature eliminates much of the tedious configuration work by implementing the Cisco Unity Client protocol. This protocol allows most VPN parameters, such as internal IP addresses, internal subnet masks, DHCP server addresses, WINS server addresses, and split-tunneling flags, to be defined at a VPN server, such as a Cisco VPN 3000 series concentrator that is acting as an IPSec server.
An Easy VPN server-enabled device can terminate VPN tunnels initiated by mobile and remote workers who are running Cisco Easy VPN Remote software on PCs. Easy VPN server-enabled devices allow remote routers to act as Easy VPN Remote nodes.
Cisco Easy Vpn Configuration
The Cisco Easy VPN client feature can be configured in one of two modes—client mode or network extension mode. Client mode is the default configuration and allows only devices at the client site to access resources at the central site. Resources at the client site are unavailable to the central site. Network extension mode allows users at the central site (where the VPN 3000 series concentrator is located) to access network resources on the client site.
After the IPSec server has been configured, a VPN connection can be created with minimal configuration on an IPSec client, such as a supported Cisco 870 series access router. When the IPSec client initiates the VPN tunnel connection, the IPSec server pushes the IPSec policies to the IPSec client and creates the corresponding VPN tunnel connection.
Note The Cisco Easy VPN client feature supports configuration of only one destination peer. If your application requires creation of multiple VPN tunnels, you must manually configure the IPSec VPN and Network Address Translation/Peer Address Translation (NAT/PAT) parameters on both the client and the server.
Configuration Tasks
Perform the following tasks to configure your router for this network scenario:
•Configure the IKE Policy
•Configure Group Policy Information
•Apply Mode Configuration to the Crypto Map
•Enable Policy Lookup
•Configure IPSec Transforms and Protocols
•Configure the IPSec Crypto Method and Parameters
•Apply the Crypto Map to the Physical Interface
•Create an Easy VPN Remote Configuration
An example showing the results of these configuration tasks is provided in the 'Configuration Example' section.
Note The procedures in this chapter assume that you have already configured basic router features as well as PPPoE or PPPoA with NAT, DCHP and VLANs. If you have not performed these configurations tasks, see Chapter 1 'Basic Router Configuration,'Chapter 3 'Configuring PPP over Ethernet with NAT,'Chapter 4 'Configuring PPP over ATM with NAT,' and Chapter 5 'Configuring a LAN with DHCP and VLANs' as appropriate for your router.
Note The examples shown in this chapter refer only to the endpoint configuration on the Cisco 870 series router. Any VPN connection requires both endpoints be configured properly to function. See the software configuration documentation as needed to configure VPN for other router models.
Configure the IKE Policy
Perform these steps to configure the Internet Key Exchange (IKE) policy, beginning in global configuration mode:
Purpose | ||
|---|---|---|
Step 1 | crypto isakmp policypriority Example: | Creates an IKE policy that is used during IKE negotiation. The priority is a number from 1 to 10000, with 1 being the highest. Also enters the Internet Security Association Key and Management Protocol (ISAKMP) policy configuration mode. |
Step 2 | encryption {des | 3des | aes | aes 192 | aes 256} Example: | Specifies the encryption algorithm used in the IKE policy. The example specifies 168-bit data encryption standard (DES). |
Step 3 | hash {md5 | sha} Example: | Specifies the hash algorithm used in the IKE policy. The example specifies the Message Digest 5 (MD5) algorithm. The default is Secure Hash standard (SHA-1). |
Step 4 | authentication {rsa-sig | rsa-encr | pre-share} Example: | Specifies the authentication method used in the IKE policy. The example specifies a pre-shared key. |
Step 5 | group {1 | 2 | 5} Example: | Specifies the Diffie-Hellman group to be used in an IKE policy. |
Step 6 | lifetime seconds Example: | Specifies the lifetime, 60-86400 seconds, for an IKE security association (SA). |
Step 7 | exit Example: | Exits IKE policy configuration mode, and enters global configuration mode. |
Configure Group Policy Information
Perform these steps to configure the group policy, beginning in global configuration mode:
Purpose | ||
|---|---|---|
Step 1 | crypto isakmp client configuration group {group-name | default} Example: | Creates an IKE policy group containing attributes to be downloaded to the remote client. Also enters the Internet Security Association Key and Management Protocol (ISAKMP) group policy configuration mode. |
Step 2 | key name Example: | Specifies the IKE pre-shared key for the group policy. |
Step 3 | dns primary-server Example: | Specifies the primary Domain Name System (DNS) server for the group. Note You may also want to specify Windows Internet Naming Service (WINS) servers for the group by using the wins command. |
Step 4 | domain name Example: | Specifies group domain membership. |
Step 5 | exit Example: | Exits IKE group policy configuration mode, and enters global configuration mode. |
Step 6 | ip local pool {default | poolname} [low-ip-address [high-ip-address]] Example: | Specifies a local address pool for the group. For details about this command and additional parameters that can be set, see the . |
Apply Mode Configuration to the Crypto Map
Perform these steps to apply mode configuration to the crypto map, beginning in global configuration mode:
Purpose | ||
|---|---|---|
Step 1 | crypto map map-name isakmp authorization list list-name Example: | Applies mode configuration to the crypto map and enables key lookup (IKE queries) for the group policy from an authentication, authorization, and accounting (AAA) server. |
Step 2 | crypto map tag client configuration address [initiate | respond] Example: | Configures the router to reply to mode configuration requests from remote clients. |
Enable Policy Lookup
Perform these steps to enable policy lookup through AAA, beginning in global configuration mode:
Purpose | ||
|---|---|---|
Step 1 | aaa new-model Example: | Enables the AAA access control model. |
Step 2 | aaa authentication login {default |list-name}method1[method2..] Example: | Specifies AAA authentication of selected users at login, and specifies the method used. This example uses a local authentication database. You could also use a RADIUS server for this. For details, see the and . |
Step 3 | aaa authorization {network | exec | commands level| reverse-access | configuration} {default |list-name} [method1[method2..]] Example: | Specifies AAA authorization of all network-related service requests, including PPP, and specifies the method of authorization. This example uses a local authorization database. You could also use a RADIUS server for this. For details, see the and . |
Step 4 | usernamename {nopassword | passwordpassword | password encryption-typeencrypted-password} Example: | Establishes a username-based authentication system. This example implements a username of Cisco with an encrypted password of Cisco. |
Configure IPSec Transforms and Protocols
A transform set represents a certain combination of security protocols and algorithms. During IKE negotiation, the peers agree to use a particular transform set for protecting data flow.
During IKE negotiations, the peers search in multiple transform sets for a transform that is the same at both peers. When such a transform set is found, it is selected and applied to the protected traffic as a part of both peers' configurations.
Perform these steps to specify the IPSec transform set and protocols, beginning in global configuration mode:
Purpose | ||
|---|---|---|
Step 1 | crypto ipsec transform-set transform-set-name transform1 [transform2] [transform3] [transform4] Example: | Defines a transform set—an acceptable combination of IPSec security protocols and algorithms. See the Cisco IOS Security Command Reference for detail about the valid transforms and combinations. |
Step 2 | crypto ipsec security-association lifetime {secondsseconds | kilobyteskilobytes} Example: | Specifies global lifetime values used when IPSec security associations are negotiated. See the Cisco IOS Security Command Reference for details. |
Note With manually established security associations, there is no negotiation with the peer, and both sides must specify the same transform set.
Configure the IPSec Crypto Method and Parameters
A dynamic crypto map policy processes negotiation requests for new security associations from remote IPSec peers, even if the router does not know all the crypto map parameters (for example, IP address).
Perform these steps to configure the IPSec crypto method, beginning in global configuration mode:
Purpose | ||
|---|---|---|
Step 1 | crypto dynamic-mapdynamic-map-name dynamic-seq-num Example: | Creates a dynamic crypto map entry and enters crypto map configuration mode. See the Cisco IOS Security Command Reference for more detail about this command. |
Step 2 | set transform-set transform-set-name [transform-set-name2..transform-set-name6] Example: | Specifies which transform sets can be used with the crypto map entry. |
Step 3 | reverse-route Example: | Creates source proxy information for the crypto map entry. See the Cisco IOS Security Command Reference for details. |
Step 4 | exit Example: | Returns to global configuration mode. |
Step 5 | crypto map map-name seq-num [ipsec-isakmp] [dynamicdynamic-map-name] [discover] [profileprofile-name] Example: | Creates a crypto map profile. |
Apply the Crypto Map to the Physical Interface
The crypto maps must be applied to each interface through which IP Security (IPSec) traffic flows. Applying the crypto map to the physical interface instructs the router to evaluate all the traffic against the security associations database. With the default configurations, the router provides secure connectivity by encrypting the traffic sent between remote sites. However, the public interface still allows the rest of the traffic to pass and provides connectivity to the Internet.
Perform these steps to apply a crypto map to an interface, beginning in global configuration mode:
Cisco Easy Vpn Remote
Purpose | ||
|---|---|---|
Step 1 | interface type number Example: | Enters the interface configuration mode for the interface to which you want the crypto map applied. |
Step 2 | crypto map map-name Example: | Applies the crypto map to the interface. See the Cisco IOS Security Command Reference for more detail about this command. |
Step 3 | exit Example: | Returns to global configuration mode. |
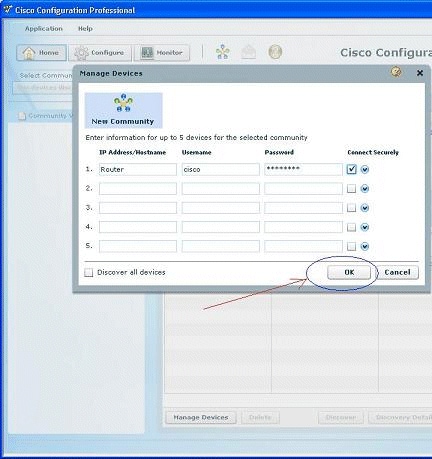
Create an Easy VPN Remote Configuration
The router acting as the IPSec remote router must create an Easy VPN remote configuration and assign it to the outgoing interface.
Perform these steps to create the remote configuration, beginning in global configuration mode:
Purpose | ||
|---|---|---|
Step 1 | crypto ipsec client ezvpnname Example: | Creates a Cisco Easy VPN remote configuration, and enters Cisco Easy VPN remote configuration mode. |
Step 2 | group group-name key group-key Example: | Specifies the IPSec group and IPSec key value for the VPN connection. |
Step 3 | peer {ipaddress | hostname} Example: | Specifies the peer IP address or hostname for the VPN connection. Note A hostname can be specified only when the router has a DNS server available for hostname resolution. |
Step 4 | mode {client | network-extension | network extension plus} Example: | Specifies the VPN mode of operation. |
Step 5 | exit Example: | Returns to global configuration mode. |
Step 6 | interfacetype number Example: Texmod mass effect 2. | Enters the interface configuration mode for the interface to which you want the Cisco Easy VPN remote configuration applied. Note For routers with an ATM WAN interface, this command would be interface atm 0. |
Step 7 | crypto ipsec client ezvpn name [outside | inside] Example: | Assigns the Cisco Easy VPN remote configuration to the WAN interface, causing the router to automatically create the NAT or port address translation (PAT) and access list configuration needed for the VPN connection. |
Step 8 | exit Example: | Returns to global configuration mode. |
Verifying Your Easy VPN Configuration
Configuration Example
The following configuration example shows a portion of the configuration file for the VPN and IPSec tunnel described in this chapter.
Easy VPN (EzVPN)
As you saw in Chapter 2, 'IPSec Overview,' for an IPSec tunnel to be established between two peers, there is a significant amount of configuration required on both peers. This includes IPSec policies, Diffie-Hellman parameters, encryption algorithms, and so on. In a large corporate environment with hundreds of sites, managing the IPSec configuration can get quite tedious. The Cisco Easy VPN feature, also known as EzVPN, eases IPSec configuration by allowing an almost no-touch configuration of the IPSec client.
EzVPN uses the Unity client protocol, which allows most IPSec VPN parameters to be defined at an IPSec gateway, which is also the EzVPN server. When an EzVPN client initiates an IPSec tunnel connection, the EzVPN server pushes the IPSec policies and other attributes required to form the IPSec tunnel to the EzVPN client and creates the corresponding IPSec tunnel connection. The tunnel on the EzVPN client can be initiated automatically or manually, or it could be traffic triggered, depending on the configuration or type of EzVPN client used. Minimal configuration is required at the EzVPN client. EzVPN provides the following general functions in order to simplify the configuration process:
Cisco Vpn Client 64 Bit Windows 10
- Negotiating tunnel parameters— This is done with encryption algorithms, SA lifetimes, and so on.
- User authentication— This entails validating user credentials by way of XAUTH.
- Automatic configuration— Performed by pushing attributes such as IP address, DNS, WINs, and so on, using MODECFG.
The Cisco Easy VPN feature supports two modes of operation:
- Client Mode
- Network Extension Mode
You will examine each of these modes in detail in the following sections.
EzVPN Client Mode
Figure 4-2 shows an IPSec Unity client configured for Client Mode in order to establish an IPSec VPN tunnel to the gateway.
EzVPN Client Mode is also known as Network/Port Address Translation (NAT/PAT) Mode. In this mode, all traffic from the client side uses a single IP address for all hosts on the private network. In Figure 4-2, all traffic from the hosts on the FastEthernet interface on the EzVPN client is translated by NAT to a source IP address of 10.0.68.5, which is assigned by the EzVPN server as an attribute using MODECFG. The client keeps track of the mappings so that it can be forwarded to the correct host on the private network.
The configuration of the EzVPN hardware client is shown in Example 4-3. Jaimini sutras pdf.
Cisco Easy Vpn Server
Example 4-3. EzVPN Client Mode Configuration
Notice that in the EzVPN client configuration, none of the IPSec policies, encryption algorithms, and so forth are configured. Example 4-4 shows how to monitor an EzVPN client configuration.
Example 4-4. Verification of EzVPN Client Mode Configuration
The configuration of the EzVPN server is shown in Example 4-5.
Example 4-5. EzVPN Server-side Configuration
Cisco Easy Vpn Client
The IOS command crypto isakmp client configuration group vpngroup defines the attributes for the VPN group that was assigned to the EzVPN client.
Network Extension Mode
Figure 4-3 shows an EzVPN client in Network Extension Mode. This mode allows the EzVPN client to present a full, routable network to the tunneled network.
Figure 4-3 EzVPN IPSec Network Extension Mode Connection
IPSec encapsulates all traffic from the EzVPN client's private network, which is marked as 'inside' to networks behind the IPSec gateway. Therefore, devices behind the gateway have direct access to devices on the EzVPN client's private network via the tunnel and vice versa without the need for NAT or PAT. As there is no reason for NAT or PAT, the EzVPN server does not push down an IP address for tunneled traffic, but all other attributes like ACLs, DNS, and WINS, can be pushed down. Example 4-6 shows the configuration of Network Extension Mode on the EzVPN client shown in Figure 4-3.
Example 4-6. EzVPN Client Configuration for Network Extension Mode
Note the ACL 100 under the mode network-extension in the configuration. The ACL 100 permits networks behind the 'inside' network (11.1.1.0/24) and allows traffic to and from these subnets to be encrypted. Without the access list, only traffic to and from the 'inside' subnet (1.1.1.0/24) is encrypted.
Redundancy is always an integral part of any IPSec design and, in the case of EzVPN dead peer detection along with backup peer list, makes such a design possible. Example 4-7 shows the client configuration with multiple EzVPN server peer addresses manually configured on the client. An alternate mechanism to provide EzVPN server redundancy is to push the backup server's address list down to the client as an attribute. Dead peer detection is on by default on the EzVPN clients.
Example 4-7. EzVPN Server Redundancy
EzVPN can be combined with XAUTH and MODECFG to provide extended authentication and thereby push all MODECFG attributes to the client. The attributes to be pushed can be defined locally on the EzVPN server or defined on a AAA server and defined either on a per-group or per-user basis. Example 4-8 shows the policies configured on a AAA server on a group basis.
Example 4-8. Per-Group–based Policy Configuration on a AAA Server
Example 4-9 shows the configuration of the policy attributes locally on the EzVPN server on a per-group basis.
Example 4-9. Per-Group EzVPN Policy Attributes Configured Locally on an EzVPN Server
You've already seen described some attributes such as IP address, WINS, DNS, and backup server in the previous section. For a complete list of attributes and their description, refer to Cisco IOS EzVPN documentation. A couple of very useful attributes for telecommuter scenarios are max-logins and include-local-lan. The max-logins attribute allows the administrator to restrict the number of simultaneous IPSec connections from the same user to the gateway. The include-local-lan attribute is very useful in scenarios in which the telecommuter's LAN has resources, such as printers, attached to the LAN and access to these resources is required when the VPN tunnel is up.
The attributes may also be applied on a per-user basis. A user attribute overrides a group attribute value. These attributes are retrieved at the time user authentication occurs using XAUTH, and are then combined with group attributes and applied during Mode-Configuration. User-based attributes are available only if RADIUS is used as the database. Example 4-10 shows the RADIUS attributes that must be configured on a per-user basis.
Example 4-10. User-Based Policy Control Using AAA
Cisco Easy Vpn Setup
Note that EzVPN using the Cisco Unity protocol is not an IETF standard. The Cisco proprietary Unity protocol is supported by Cisco IOS devices, VPN 3000, and PIX devices for interoperability across Cisco devices.
